Definition
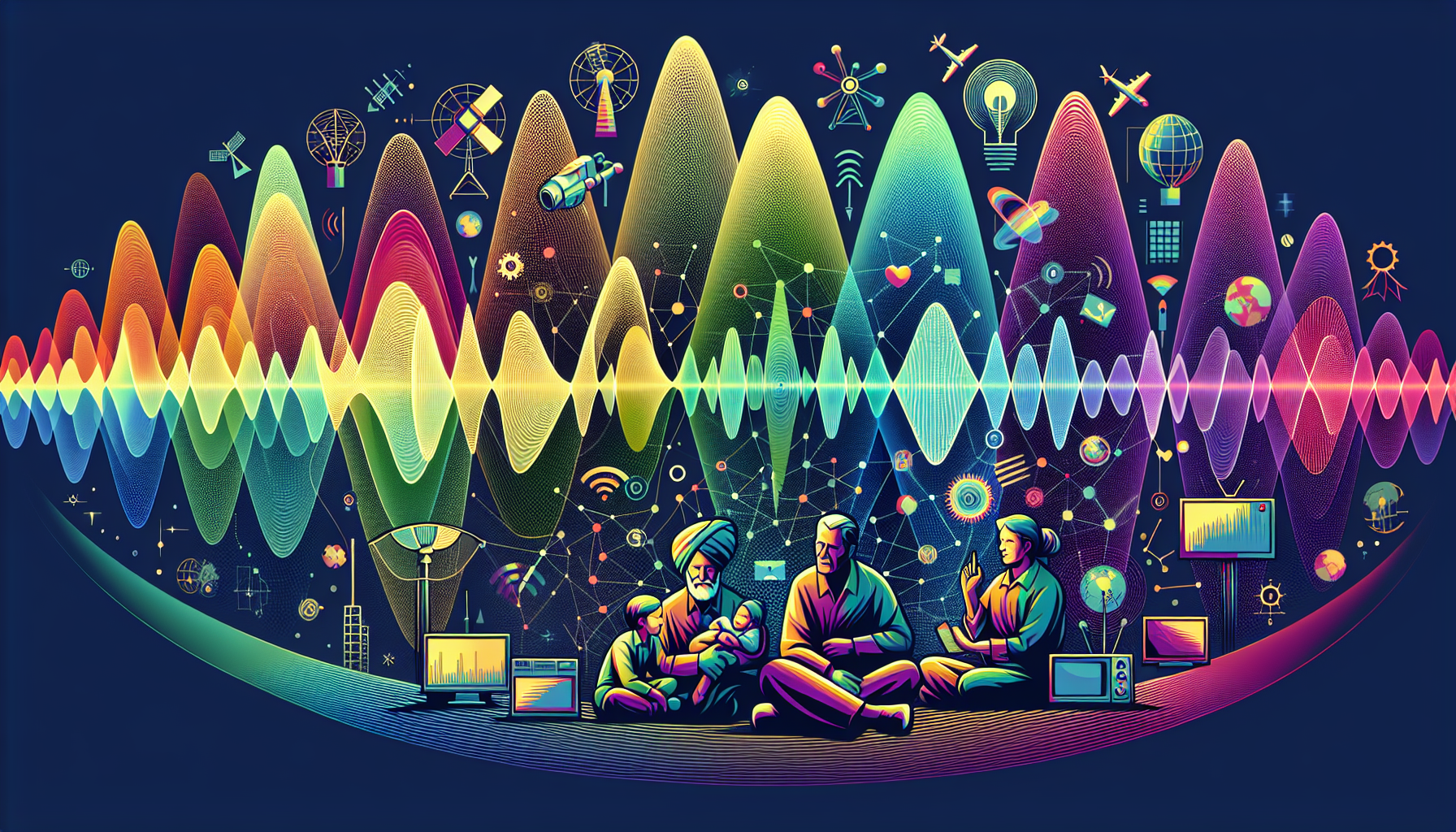
Electromagnetic Spectrum Control (EMSC) refers to the process implemented by the military to manage and coordinated use of the electromagnetic spectrum. This range encompasses frequencies used for transmissions in radio, radar, and television signals to facilitate effective communication and operations. The aim is to prevent interference and allow forsmooth communication and control during missions.
Key Takeaways
- Electromagnetic Spectrum Control (EMSC) is a critical aspect of modern military operations, often considered as a strategic asset in the battlefield. It is aimed at exploiting, attacking, protecting and managing resources within the Electromagnetic Spectrum (EMS) in line with executed operational tasks.
- EMSC involves activities across the spectrum, including electronic warfare, frequency management, and signals intelligence. Through effective EMSC, forces can disrupt enemy communications, avoid detection, gather intelligence, and ensure their own communications are effective and secure.
- Since the EMS is a finite resource and it is available to both friendly and enemy forces, uncontrolled or improper utilization may lead to inadvertent and undesired interference. Hence the objective of EMSC is to control or dominate an electromagnetic environment to ensure it works to the offender’s advantage while disadvantaging the competitor to ensure mission success.
Importance
Electromagnetic Spectrum Control (EMSC) is critically important in military operations due to its strategic role in communication, surveillance, and weapon systems.
The electromagnetic spectrum, which includes forms of energy like radio waves, microwaves, infrared, visible light, ultraviolet light, X-rays, and gamma rays, forms the backbone of modern digital communication and technology.
The ability to control or dominate this spectrum gives a military force significant advantage, allowing for reliable and secure communication, effective electronic warfare, and interference with enemy systems.
In contrast, a lack of EMSC may impair a force’s effectiveness by impeding communication, giving the enemy opportunities for surveillance or electronic attacks, or disrupting weapon systems that rely on the electromagnetic spectrum, which ultimately can alter the outcomes of military engagements.
Explanation
The purpose of Electromagnetic Spectrum Control (EMSC) in military operations is to optimize the use of the electromagnetic spectrum, which includes all possible frequencies of electromagnetic radiation, for various military purposes. The goal of EMSC is to ensure that our forces have unrestricted access to the electromagnetic spectrum to support the effective application of force, while simultaneously denying and degrading the use of the spectrum by adversary forces.
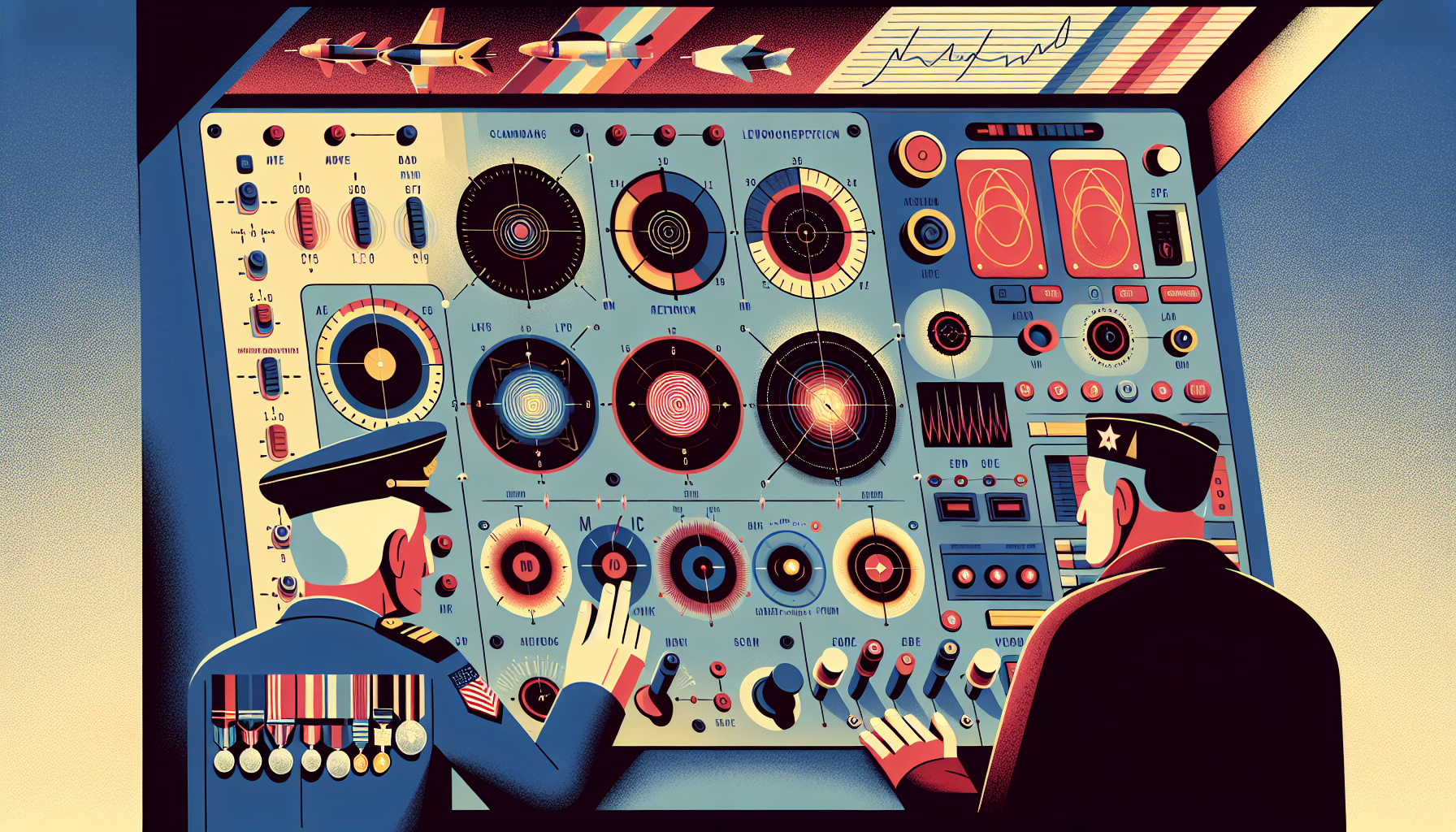
This is crucial because modern warfare employs various spectrum-dependent systems like radars, communication networks, guidance systems, and electronic warfare systems which are essential for situational awareness, command and control, and precision strike capabilities. EMSC is used for various critical operations in the military.
It encompasses a vast array of activities like planning, coordinating, and managing the use of the electromagnetic spectrum, including the operational aspects such as command, control, and communications, intelligence, surveillance and reconnaissance (ISR), and electronic warfare. The electromagnetic spectrum is used during operations to enhance the force’s ability to communicate and gather intelligence effectively, and for targeting and engaging with the enemy.
By controlling and dominating the electromagnetic spectrum, the military forces can interfere with the enemy’s command and control capabilities, jam their communications, deceive their radar and surveillance systems, and disrupt their ability to effectively conduct operations. Hence, EMSC serves a pivotal function in gaining superiority in the battlefield.
Examples of Electromagnetic spectrum control (EMSC)
Operation Desert Storm: During the Gulf War, the U.S. military extensively used electromagnetic spectrum control to disrupt and overpower Iraq’s integrated air defense systems. This included jamming radars, communications interception, and deception techniques.
U.S. and NATO operations in Yugoslavia (1999): Here, the EMSC was used to degrade Yugoslav air defenses, including the use of electronic warfare systems to jam communications and radar systems, as well as the deployment of decoys to confuse enemy’s defensive networks.
Modern Warfare Drone Use: In various global conflicts today, drones are increasingly used to gain control over the electromagnetic spectrum. This includes the use of signals intelligence (SIGINT) drones to intercept and jam enemy communications, as well as the use of active electronically scanned array (AESA) radars for air-to-air and air-to-ground missions. These platforms allow the military to dominate the electromagnetic spectrum, effectively disrupting enemy operations while ensuring friendly forces can communicate and execute missions effectively.
FAQs about Electromagnetic Spectrum Control (EMSC)
What is Electromagnetic Spectrum Control (EMSC)?
Electromagnetic Spectrum Control, often referred to as EMSC, is a military operational strategy where forces seek to control the electromagnetic spectrum (EMS). This includes actively emitting, passively receiving, and denying adversaries access to the EMS during an operation.
Why is EMSC important in military operations?
EMSC plays a crucial role in ensuring command over communication channels, electronic warfare, intelligence, and surveillance. Its primary purpose is to assure our forces effective electromagnetic spectrum use while denying adversaries the same capability.
What are the key strategies for EMSC?
EMSC involves a combination of resources and strategies including Electronic Attack (EA), Electronic Protection (EP), and Electronic Support (ES). Combined together, these strategies protect our infrastructure while disrupting rivals’ communications and operations.
How does EMSC provide situational awareness?
EMSC provides situational awareness by detecting, identifying, and locating sources of intentional and unintentional radiated electromagnetic energy in the operational environment. It significantly aids in understanding threats and enhances tactical decision making.
How does the military train for EMSC?
The military personnel undergo extensive training to maintain deep expertise in the electromagnetic spectrum and various supporting technologies. This includes rigorous training in electronic warfare and communications systems and strategies.
Related Military Operation Terms
- Electromagnetic Interference (EMI)
- Frequency Allocation
- EMSC Regulations
- Radio-Frequency Management
- Spectrum Management Authority
Sources for More Information
- Military & Aerospace Electronics
- U.S. Department of Defense
- Defense Advanced Research Projects Agency (DARPA)
- Armed Forces Communications and Electronics Association (AFCEA)
 Benefits.com Advisors
Benefits.com Advisors
With expertise spanning local, state, and federal benefit programs, our team is dedicated to guiding individuals towards the perfect program tailored to their unique circumstances.
Rise to the top with Peak Benefits!
Join our Peak Benefits Newsletter for the latest news, resources, and offers on all things government benefits.